FinFisher surveillanceware has been upgraded to infect Windows devices using a UEFI (Unified Extensible Firmware Interface) bootkit making use of a trojanized Windows Boot Manager, marking a shift in infection vectors that allow it to elude discovery and analysis.
Detected since 2011, FinFisher also known as the Wingbird of FinSpy is a spyware toolset for Windows, macOS, and Linux developed by Anglo-German firm Gamma International and supplied exclusively to law enforcement and intelligence agencies. But like with NSO Group’s Pegasus, the software has also been used to spy on Bahraini activists in the past allegedly and delivered as part of spear-phishing campaigns in September 2017.
The FinFisher is capable of harvesting user credentials, sensitive documents, log keystrokes, tap email messages from Thunderbird, Outlook, Apple Mail and Icedove, intercept Skype contacts, chats, calls and transferred files.
While the tool was previously deployed through tampered installers of legitimate applications such as TeamViewer, VLC, and WinRAR that were backdoored with an obfuscated downloader, subsequent updates in 2014 enabled infections via Master Boot Record (MBR) bootkits with the goal of injecting a malicious loader in a manner that’s engineered to slip past security tools.
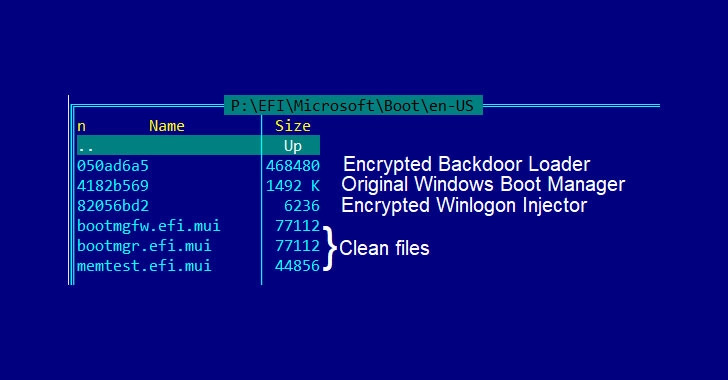
It now features the ability to deploy a UEFI bootkit to load FinSpy, with new samples exhibiting properties that replaced the Windows UEFI boot loader with a malicious variant and boasts of a four layered obfuscation and detection-evasion methods to slow down reverse engineering and analysis.
“This way of infection allowed the attackers to install a bootkit without the need to bypass firmware security checks,” Kaspersky’s Global Research and Analysis Team (GReAT) said in a technical deep dive following an eight-month-long investigation. “UEFI infections are very rare and generally hard to execute, they stand out due to their evasiveness and persistence.”
The UEFI is a publicly available specification that defines a software interface between an operating system and platform firmware. UEFI replaces the legacy Basic Input/Output System (BIOS) firmware interface originally present in all IBM PC-compatible personal computers. However due to the fact that UEFI facilitates the loading of the operating system itself, bootkit infections are not only resistant to OS reinstallation or replacement of the hard drive but are also inconspicous to security solutions running within the operating system.
Thus enabling threat actors to have control over the boot process, achieve persistence, and bypass all security defences. “While in this case the attackers did not infect the UEFI firmware itself, but its next boot stage, the attack was particularly stealthy, as the malicious module was installed on a separate partition and could control the boot process of the infected machine,” the researchers added.