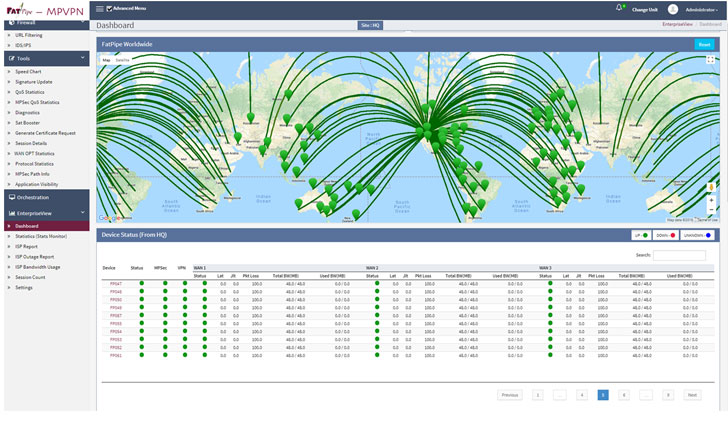
The FBI has disclosed that a yet to be identified threat actor has been exploiting a previously known weakness in the FatPipe MPVPN networking devices at least since May 2021 using it to obtain initial foothold as well as maintain persistent access into the vulnerable networks.
This allowed APT actors to gain unrestricted file upload function to drop a web shell for exploitation activity with root access and this has served as a jumping point into other infrastructure for the APT actors.
In other words, the zero-day vulnerability enables a remote attacker to upload a file to any location on the filesystem on an affected device. The security flaw impacts the web management interface of FatPipe WARP, MPVPN, and IPVPN router clustering and VPN load-balancing devices running software prior to the latest version releases 10.1.2r60p93 and 10.2.2r44p1.
The alert also indicated that the threat actor leveraged the web shell to move laterally and strike additional U.S. infrastructure by creating malicious SSH service and a few other steps to hide their intrusion and protect the exploit till it is needed again.
In an independent bulletin (FPSA006), FatPipe said that the bug stems from a lack of input validation mechanism for specific HTTP requests, thus enabling an attacker to exploit the issue by sending a specially crafted HTTP request to the affected device.
There is currently no workarounds but simple mitigation tips could be disabling UI and SSH access on the WAN or better still setting up an Access List to permit access from only trusted sources.